Trezor Suite | Official Trezor™ Wallet Setup & Crypto Security Guide™
Trezor Suite is the all-in-one platform developed by SatoshiLabs to manage, secure, and interact with your cryptocurrency using the Trezor hardware wallet. It offers a clean, secure, and intuitive interface where users can send, receive, and trade crypto assets while maintaining full control of their private keys. The Suite is available both as a desktop application and a secure web version, ensuring accessibility without compromising safety.
Why Choose Trezor Suite?
With the rise of digital currencies, online threats have also multiplied. Phishing scams, malware, and fake wallet apps often target users who store keys or recovery phrases on compromised devices. Trezor Suite eliminates this risk by requiring physical confirmation for every transaction through your hardware wallet. It acts as a bridge between your device and the blockchain, making it nearly impossible for hackers to intercept or alter your transactions.
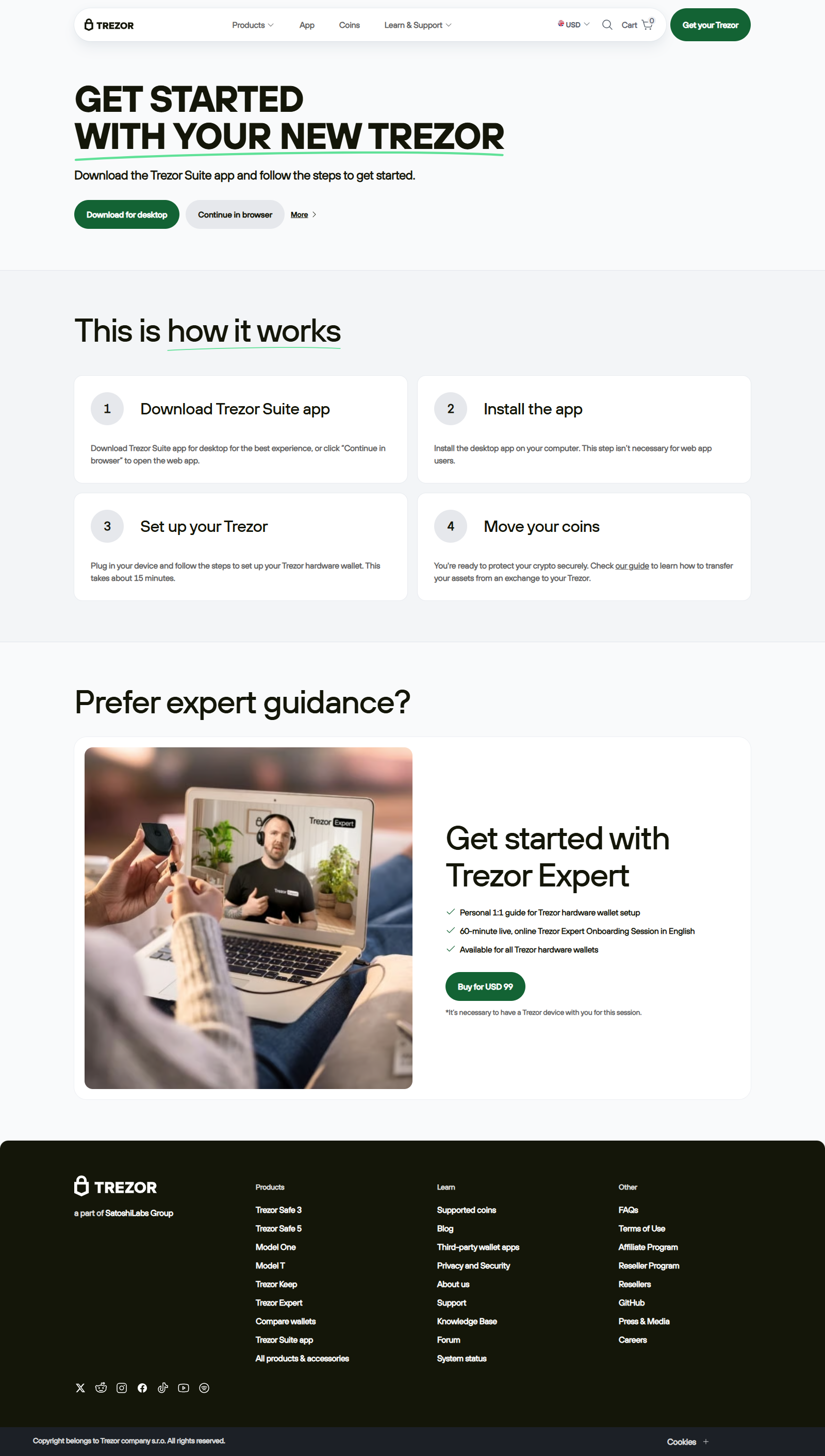
Getting Started with Trezor Suite
To begin, visit the official Trezor website and download Trezor Suite for your operating system (Windows, macOS, or Linux). Always ensure you’re downloading from https://trezor.io to avoid counterfeit software. Once installed, connect your Trezor hardware wallet using the provided USB cable. The Suite automatically detects your device and prompts you to either create a new wallet or recover an existing one using your seed phrase.
During setup, the software will guide you through creating a PIN and securely backing up your 12- or 24-word recovery seed. This recovery seed is the cornerstone of your crypto security—it’s the only way to restore access if your device is lost or damaged. Write it down on the provided recovery card, never photograph or digitize it, and store it offline in a fireproof, water-resistant location.
Advanced Security Features
Trezor Suite integrates several cutting-edge security mechanisms. One such feature is passphrase protection, also called the “25th word.” This optional layer adds an extra phrase on top of your seed, effectively creating hidden wallets. Even if someone gains access to your recovery seed, they won’t be able to access funds in hidden accounts without the exact passphrase. Remember, each unique passphrase creates a completely separate wallet—so handle it with care.
Another valuable function is transaction verification. Every transaction you initiate through Trezor Suite must be confirmed physically on your Trezor device’s screen. This ensures that what you see on your computer matches what’s being signed, protecting you from phishing sites or malicious browser extensions that could attempt to redirect funds.
Managing Crypto Assets
Inside Trezor Suite, you can manage multiple assets, including Bitcoin, Ethereum, Litecoin, Cardano, and hundreds of ERC-20 tokens. The dashboard displays a clear overview of your portfolio, recent activity, and market values. Users can easily switch between fiat and crypto denominations to track performance. Trezor Suite also supports direct exchange integrations, allowing secure swaps between assets without transferring funds to third-party platforms.
Privacy and Connectivity
Privacy is a central philosophy of Trezor Suite. Users can connect to the Bitcoin network via their own node or through a trusted remote server. For added privacy, Tor connectivity can be enabled directly in the settings, helping you hide your IP address and reduce data exposure. The Suite also supports labeling features, where you can assign transaction labels and notes that sync privately with your encrypted storage—not with cloud servers.
Firmware and Updates
Firmware updates are periodically released to improve compatibility, performance, and security. The Suite notifies users when a new version is available and provides guided steps for a safe update. Always verify firmware signatures and never install updates from unofficial sources. Trezor’s open-source code ensures transparency and allows independent security audits from the global crypto community.
Backup and Recovery Planning
In addition to your recovery seed, consider creating a metal backup using a steel plate to resist physical damage. Some users also maintain redundant backups stored in different locations to prevent total loss from disasters. For high-value holdings, explore multisignature setups that require multiple devices or users to approve transactions, providing an extra safeguard against theft or misuse.
Best Practices for Long-Term Security
1. Always verify URLs and SSL certificates before connecting your device. 2. Never share your recovery seed, PIN, or passphrase with anyone—including support agents. 3. Keep your Trezor device firmware and Suite application updated. 4. Use a strong, unique PIN and enable passphrase protection for sensitive wallets. 5. Conduct regular security audits and test your recovery process with small amounts. 6. Avoid public Wi-Fi when handling cryptocurrency transactions. 7. Bookmark the official site to prevent phishing attempts.
Conclusion
Trezor Suite stands as a benchmark for secure, user-friendly cryptocurrency management. Its intuitive interface, hardware-level security, and open-source transparency make it ideal for beginners and advanced users alike. By combining hardware protection with disciplined backup and privacy practices, you ensure that your digital wealth remains under your control for years to come.
As the crypto landscape continues to evolve, staying informed and cautious remains essential. Trezor Suite provides all the tools necessary to navigate this ecosystem confidently, reinforcing the foundational principle of crypto: “Not your keys, not your coins.” With Trezor Suite and a proactive approach to security, your digital assets are truly protected.